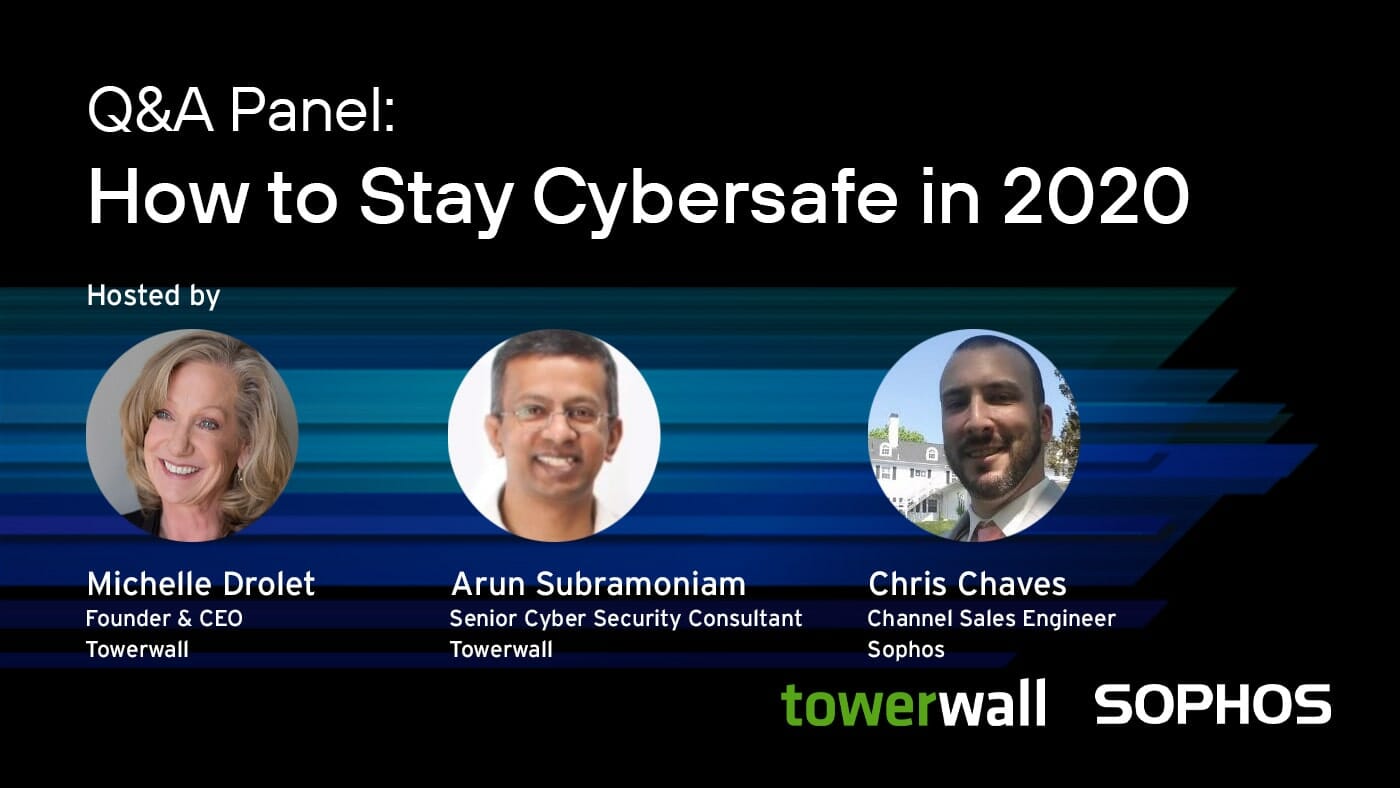
Michelle Drolet
The COVID-19 pandemic has brought about a seismic shift in how the world goes to work. Apart from essential services, remote work is the new normal, mandated everywhere — even in organizations that never previously offered remote work options. Lack of VPN infrastructure or its ability to scale, legacy systems that were never designed for remote work,
4 Minute 53 Second Read