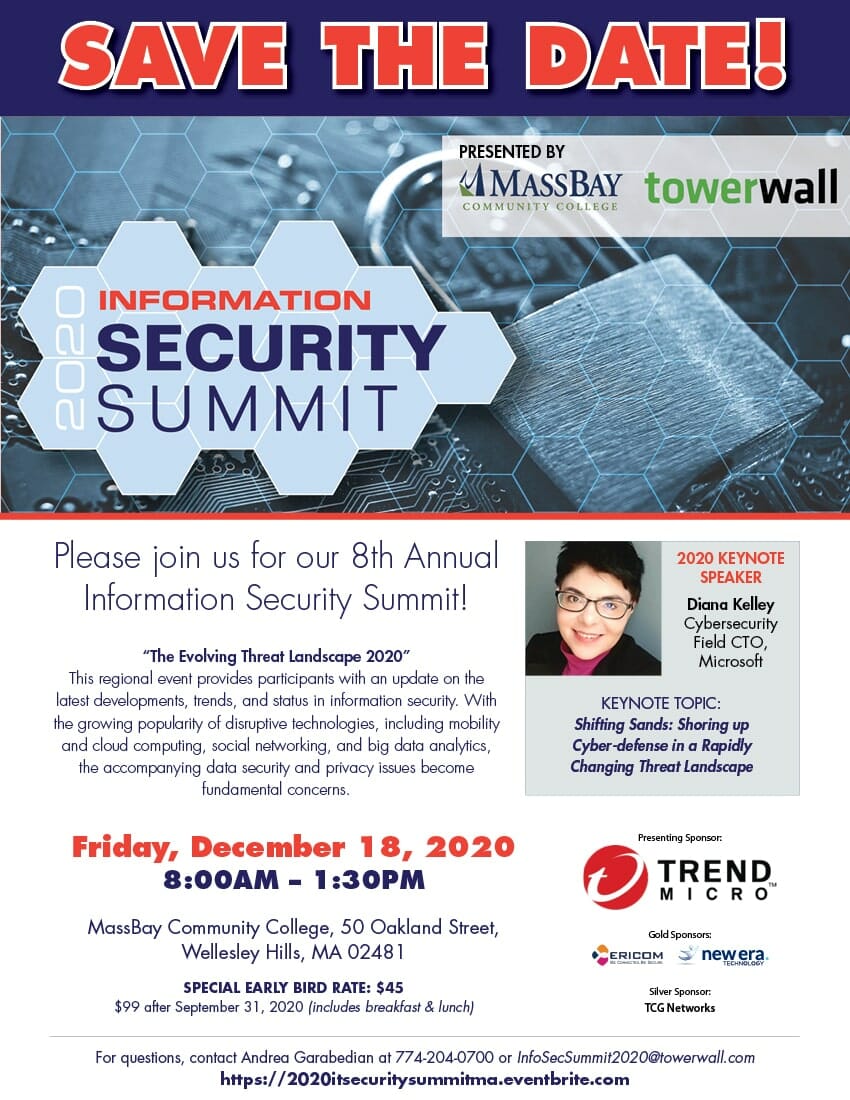
Please join us for our 8th Annual Information Security Summit! “The Evolving Threat Landscape 2020” This regional event provides participants with an update on the latest developments, trends, and status in information security. With the growing popularity of disruptive technologies, including mobility and cloud computing, social networking, and big data analytics, the accompanying data security
0 Minute 45 Second Read








